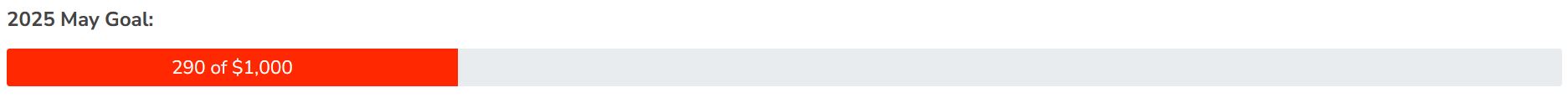
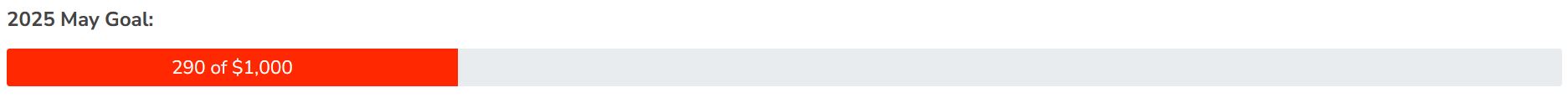
Your Donations Help Support the NTP Community --
Bugzilla – Main Page
version 5.0.6
- Home
- | New
- | Browse
- | Search
- | [?]
- | Reports
- | Requests
- | New Account
- | Log In
- | Forgot Password
ntp-4.2.8p18 was released on 25 May 2024 and addresses 40 bugs and provides 40 improvements.
Please see the NTP 4.2.8p18 Changelog for details.
| Release | Version | Date | Download | ChangeLog |
|---|---|---|---|---|
| Stable | 4.2.8p18 | 2024/05/25 | https/md5 | https |
| Development | 4.3.105 | 2024/05/25 | https/md5 | https |
This Bugzilla provides tracking of development issues (e.g. bugs, enhancements) for the Network Time Protocol (NTP) Reference Implementation produced by the NTP Project.
Please report security related bugs by PGP-encrypted email to the NTF Security Officer Team. You can use our NTF Security Officer Key. PLEASE DO NOT ENTER SECURITY RELATED REPORTS IN THIS BUG TRACKING SYSTEM.
Please use the NTP Mailing Lists for discussions of NTP-related matters which are not development issues.